¶ adPEAS
https://github.com/61106960/adPEAS
¶ About
adPEAS is a Powershell tool to automate Active Directory enumeration. In fact, adPEAS is like a wrapper for different other cool projects like:
- PowerView
- Empire
- Bloodhound
As said, adPEAS is a wrapper for other tools. They are almost all written in pure Powershell but some of them are included as compressed binary blob or C# code.
adPEAS-Light is a version without Bloodhound and vulnerability checks and it is more likely that it will not blocked by an AV solution.
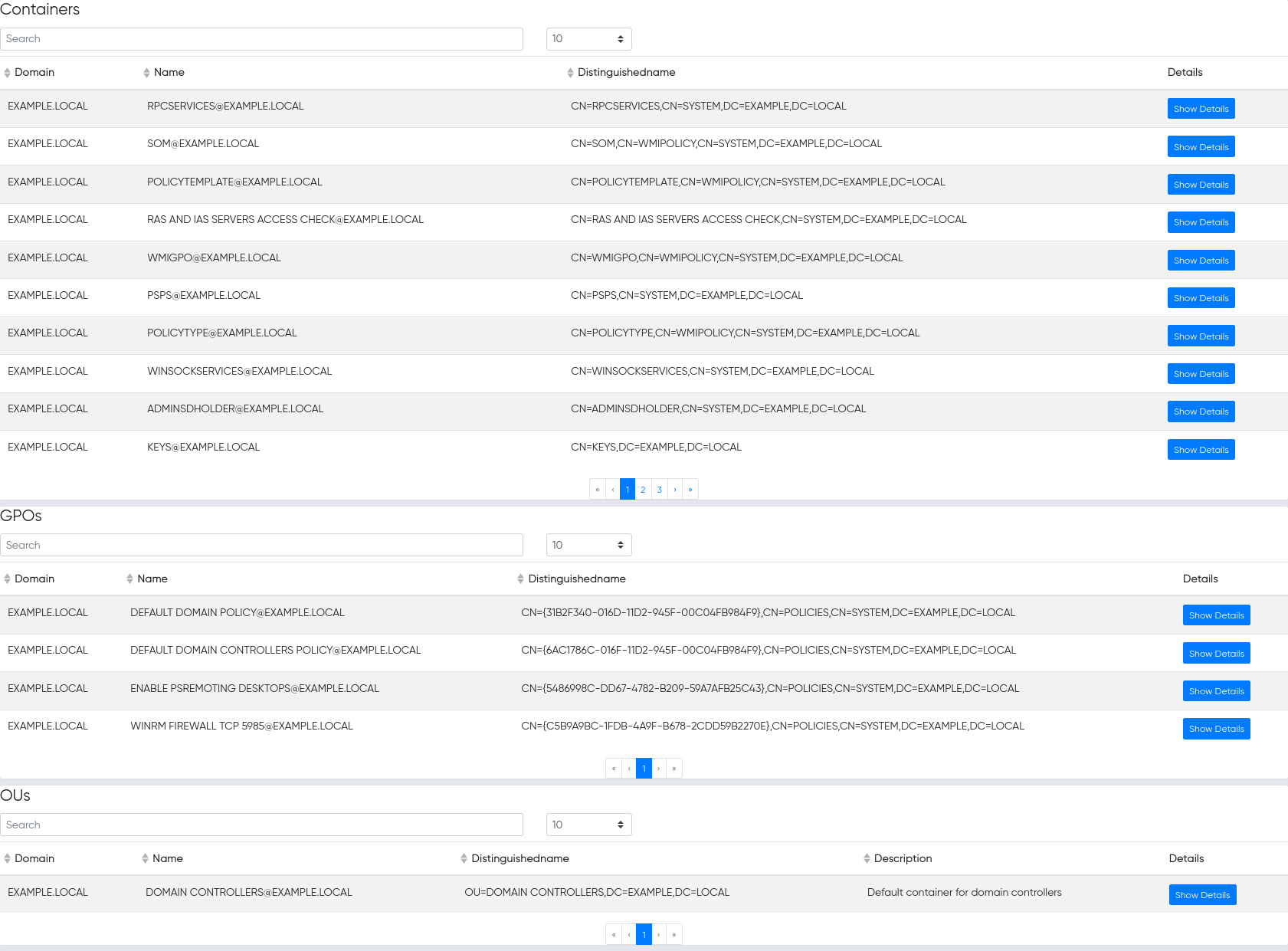
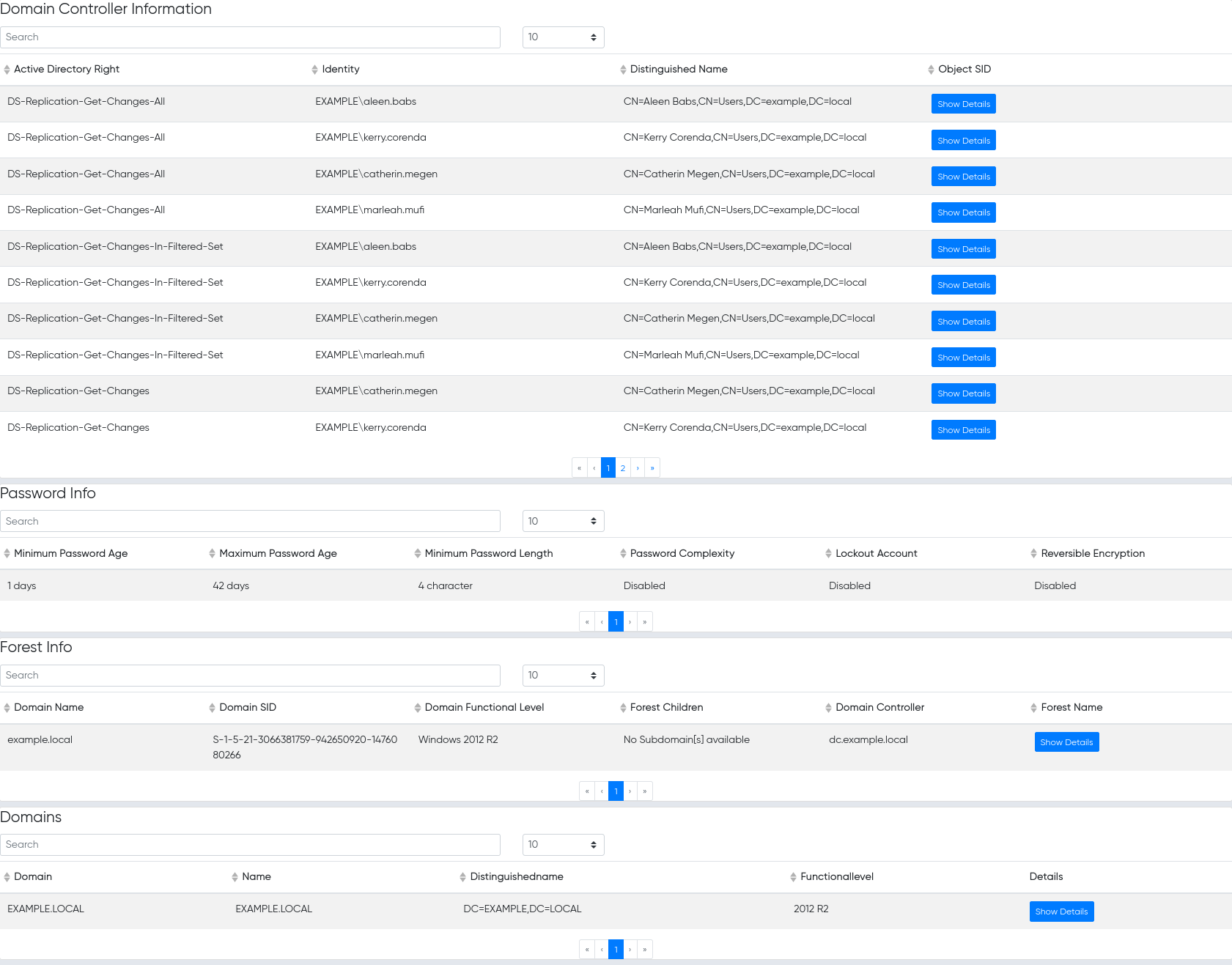
¶ Screenshots of results
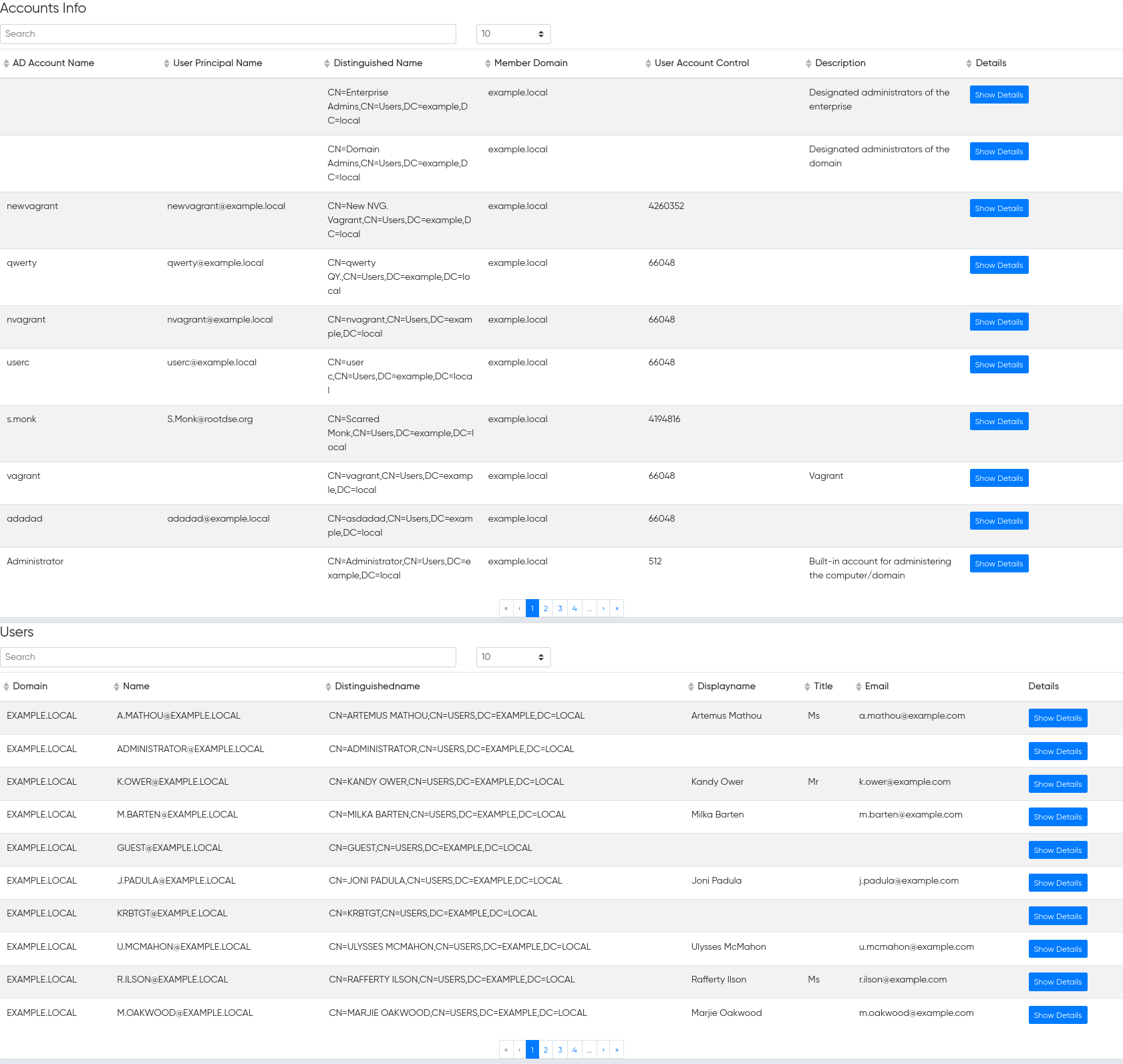
¶ Users
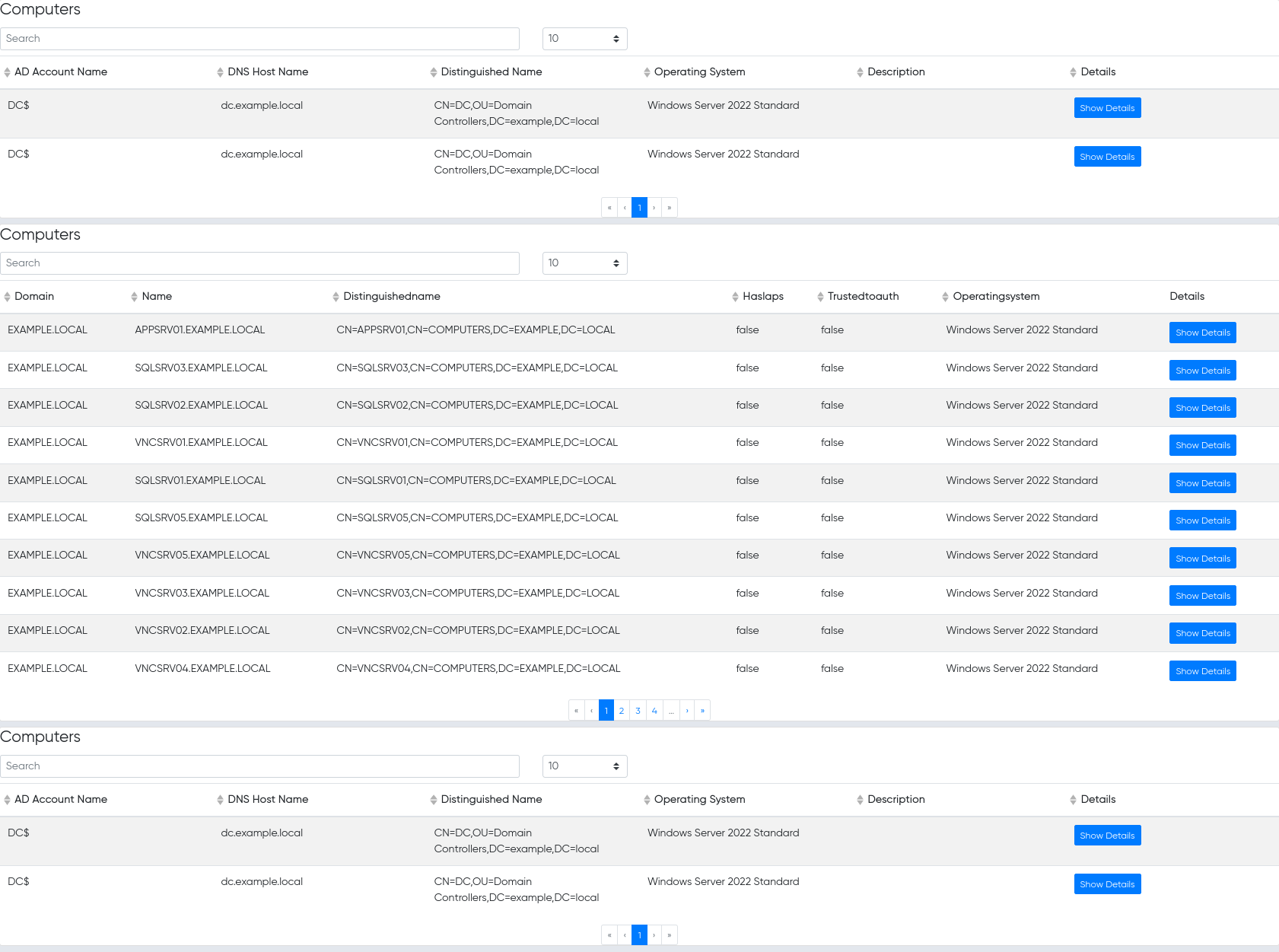
¶ Computers
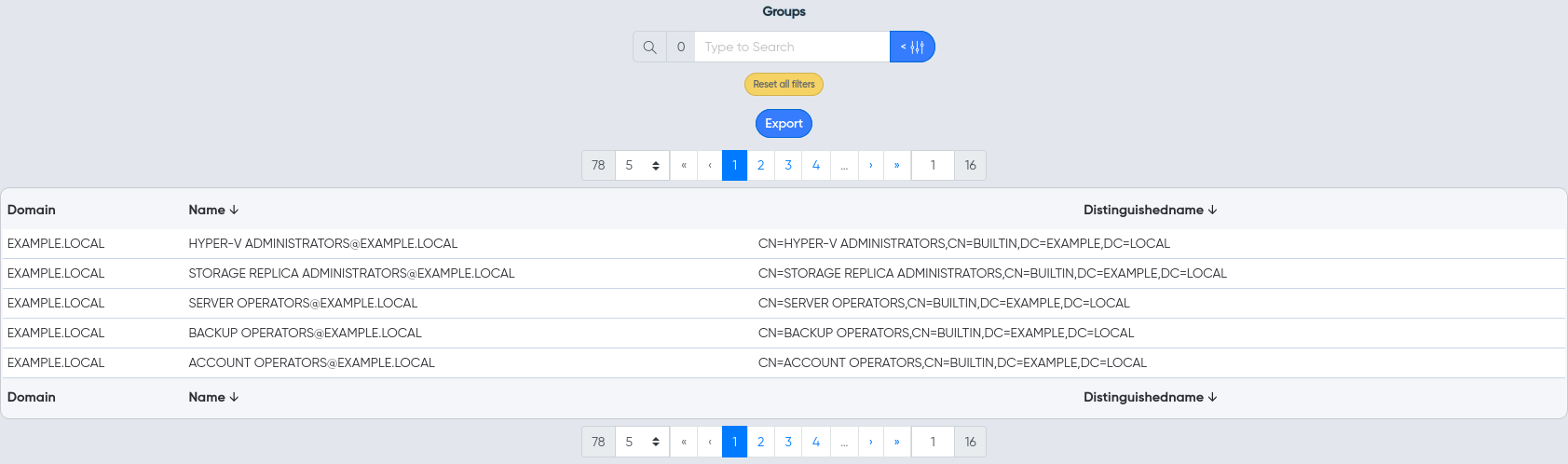
¶ Groups
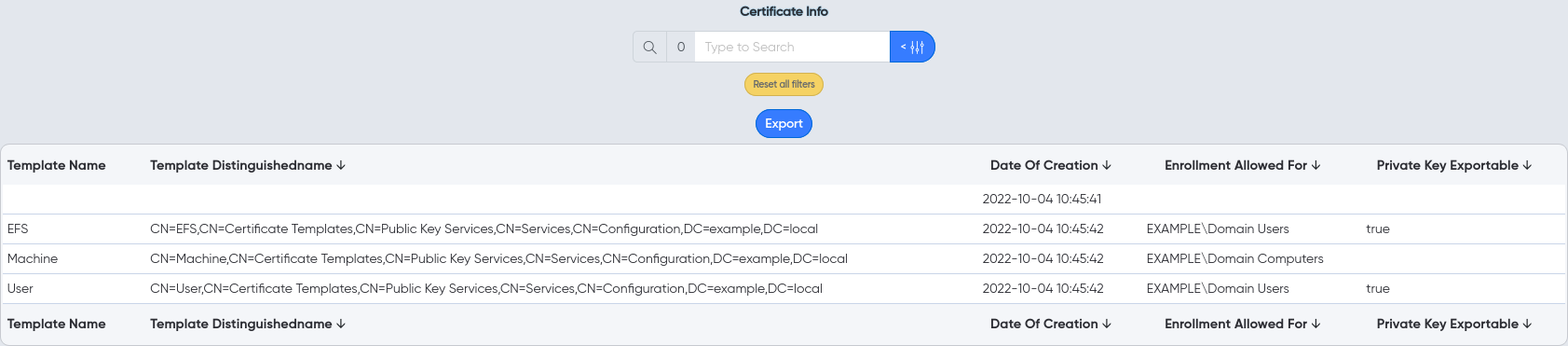
¶ Certificates
¶ Other
¶ Host
¶ How to start?
You can find this here.